DDoS Attack Examples and How to Mitigate Them
- Updated: Jun 13, 2025
- 11 min
All electronic systems have a limited data processing capacity. Typically, this threshold is never exceeded under normal conditions.
However, that can change when anomalous activity kicks in. A distributed denial-of-service (DDoS) attack is a strategy that can drain a web server’s resources and disrupt the associated online service.
Usually, Node.js developers manage to protect servers. However, not all startups have full in-house development teams. So, spreading awareness about DDoS attacks is necessary to help safeguard businesses.
DDoS attacks emerged in the mid-1990s as an ideological weapon that groups like Anonymous and similar hacktivists used. Over time, the motivations have expanded from script kiddies looking to satisfy their egos and get an adrenaline rush to unscrupulous businesses trying to undermine their competition.
The latest trend is extortion through so-called “ransom DDoS” attacks. Here, an adversary threatens to knock an organization’s website offline unless it pays a crypto ransom.
This article summarizes known DDoS attack methods and discusses effective countermeasures.
Guard against downtime and data breaches with our expert DDoS protection tailored to your business needs — contact us today to get started!
Why DDoS Attacks Are So Dangerous
DDoS (Distributed Denial of Service) attacks flood a website or server with too much traffic, causing it to crash or slow down. This makes it impossible for real users to access the site. It can hurt businesses and damage trust. In 2023, Google stopped a DDoS attack that peaked at 398 million requests per second — the largest example of DDoS attacks ever recorded.
These attacks are dangerous because they’re cheap to launch but costly to stop. Hackers often use networks of infected devices, called botnets, to carry out attacks. During an attack, online stores can lose thousands of dollars per minute in missed sales. DDoS can also be a distraction, hiding more serious hacks happening at the same time. Hospitals, banks, and governments have all been targeted, putting critical services at risk.
An extra concern is that DDoS operators are increasingly adept at amplifying their attacks via huge botnets consisting of unsecured IoT devices. This approach was behind the most powerful assaults reported to date, including the DDoS example in 2016, when the Dyn cyber-attack generated rogue attack traffic exceeding 1 Tbps.
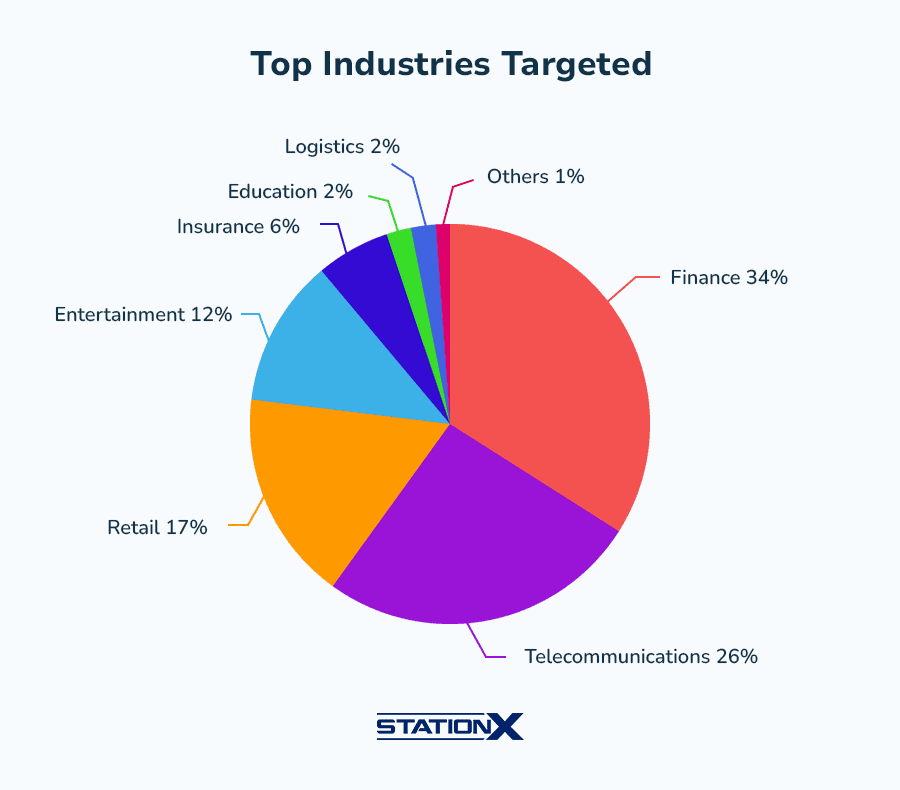
Common DDoS Attack Targets In 2025
With the COVID-19 crisis being underway, the implementation of remote learning programs saw a dramatic spike this year, and so did DDoS attacks targeting the education and academic sector.
Mostly orchestrated by hacktivists and rebellious students, these incursions lead to network downtime and disrupt virtual classes.
There was also an increase in unwanted intrusions and malware infections in Mac and other devices used in day-to-day work.
Unethical business competition is another area where DDoS plays a role. For instance, malicious actors often swamp Minecraft servers to lure gamers into switching to another hosting service.
During January through June 2023, compared to the same period in 2012, the number of DDoS attacks sized 100 Gbps and above grew an enormous 275%.
At the same time, the number of small attacks, sized 5 Gbps and below, also grew by more than 200%.
Here are the most targeted DDoS attack industries, according to statistics from Cisco Systems:
| DDoS attack target sector | Why targeted? | Potential impact |
|---|---|---|
| Cloud Services (AWS, Azure, Google Cloud) | High-value disruption; affects thousands of dependent businesses. | Widespread outages for SaaS products, APIs, and websites. |
| Banks & Financial Institutions | Extortion, fraud cover, or hacktivism. Disrupting transactions = direct profit loss. | Frozen payments, stock market delays, customer distrust. |
| E-Commerce & Retail | Peak sales periods (Black Friday) maximize damage. | Millions in lost revenue per minute of downtime. |
| Government & Critical Infrastructure | Political motives, cyberwarfare, or chaos creation. | Disrupted emergency services, elections, or utilities. |
| Gaming & Esports | Competitive sabotage or streamer harassment. | Server crashes, ruined tournaments, lost ad revenue. |
| Telecoms & ISPs | Crippling ISPs causes mass internet blackouts. | Businesses, hospitals, and homes lose connectivity. |
| Healthcare Systems | Ransom opportunities (life-or-death pressure). | Delayed patient care, leaked medical records. |
| News & Media Sites | Censorship or silencing dissent during crises. | Misinformation spreads if trusted sources are down. |
| Education Platforms | Disrupt exams, admissions, or remote learning. | Student data breaches, canceled online tests. |
Common Types of DDoS Attacks
In 2022, there was a 74% YoY increase in the number of DDoS attacks.
Security professionals identify numerous denial-of-service attack types that differ in the logic of triggering a denial-of-service condition. Here are the most common types of DDoS attacks:
1. Volumetric Attacks (Flood Attacks)
These types of denial of service attacks saturate the target’s bandwidth with massive internet traffic:
- UDP Flood – Exploits User Datagram Protocol (UDP) packets to flood random ports.
- ICMP Flood (Ping Flood) – Overwhelms the target with ICMP Echo Request (ping) packets.
- DNS Amplification – Exploits open DNS resolvers to send large responses to a victim.
- NTP Amplification – Abuses Network Time Protocol (NTP) servers to flood targets.
2. Protocol Attacks (Network Layer Attacks)
Protocol DDoS attacks are malicious attempt that exploit weaknesses in network protocols:
- SYN Flood – Sends excessive TCP SYN requests, exhausting connection tables.
- Ping of Death – Sends malformed/oversized ICMP packets to crash systems.
- Smurf Attack – Uses spoofed ICMP packets to trigger a broadcast storm.
- Slowloris – Opens many HTTP connections but keeps them open as long as possible.
3. Application Layer Attacks (Layer 7 Attacks)
Target web applications by mimicking legitimate traffic:
- HTTP Flood – Overloads servers with HTTP GET/POST requests (can be low-and-slow).
- DNS Query Flood – Sends excessive DNS requests to take down DNS servers.
- WordPress Pingback Attack – Exploits XML-RPC pingbacks to create traffic loops.
- RUDY (R-U-Dead-Yet?) – Submits long-form fields very slowly to exhaust server resources.
SYN Flood
This foul play abuses the TCP three-way handshake, a fundamental mechanism used to set up a connection between a client, a host, and a server in the TCP protocol framework. Criminals flood a target server with multiple SYN (synchronize) packets coming from a rogue IP. For the record, the role of SYN packets in a benign scenario is to request a connection with a server.
Fraggle Attack
This attack vector involves rogue UDP packets carrying a knockoff IP address of the target’s router.
As a result, the network device replies to itself nonstop until it becomes incapable of reacting to legitimate users’ requests.
LAND Attack
LAND – short for Local Area Network Denial – is a raid relying on dodgy SYN packets in which the source IP and the destination IP are an exact match.
The victim server is thereby pulled into a loop of iterative responses to itself, which causes a denial-of-service predicament.
Slowloris
An attacker initiates a bevy of simultaneous connections to a web server and keeps them active by periodically adding split packets and HTTP headers.
These connections stay uncompleted for a long time and waste the server’s processing capacity. On a side note, a single computer can be enough to execute the Slowloris onslaught.
Low Orbit Ion Cannon (LOIC)
Ideally, LOIC is used as a tool that allows security experts to identify the pain points of a network connection by stress-testing it.
However, sometimes criminals turn the original purpose upside down by mishandling it to deplete a server’s resources with fake HTTP, UDP, and TCP packets.
High Orbit Ion Cannon (HOIC)
This is a LOIC spin-off with a much higher stress-testing potential under its hood.
DDoS actors often hinge on it to generate myriads of HTTP POST and GET requests and knock a target server offline in a snap. Incidentally, HOIC can concurrently home in on more than 250 domains.
APDoS
The acronym stands for “Advanced Persistent Denial-of-Service”. This mechanism kicks in when attackers blend a series of different techniques to deteriorate the performance of a network or a server.
Another hallmark of this attack is that it usually lasts for weeks and withstands traditional incident response methods.
IoT Botnet Attack
This is one of the most destructive types of DDoS as it can generate immense data transfer rates that reach several terabits per second.
These attacks parasitize a network of compromised Internet of Things (IoT) devices to generate malicious traffic and route it toward a computer network.
Cloudflare DDoS Threat Report indicates that network-layer DDoS attacks are the most common.
In Q1, it blocked 20.5 million attacks. Of those, 16.8 million hit the network layer.
About 6.6 million targeted Cloudflare directly, and another 6.9 million went after its protected service providers. These numbers show how frequent and serious network-layer attacks have become. 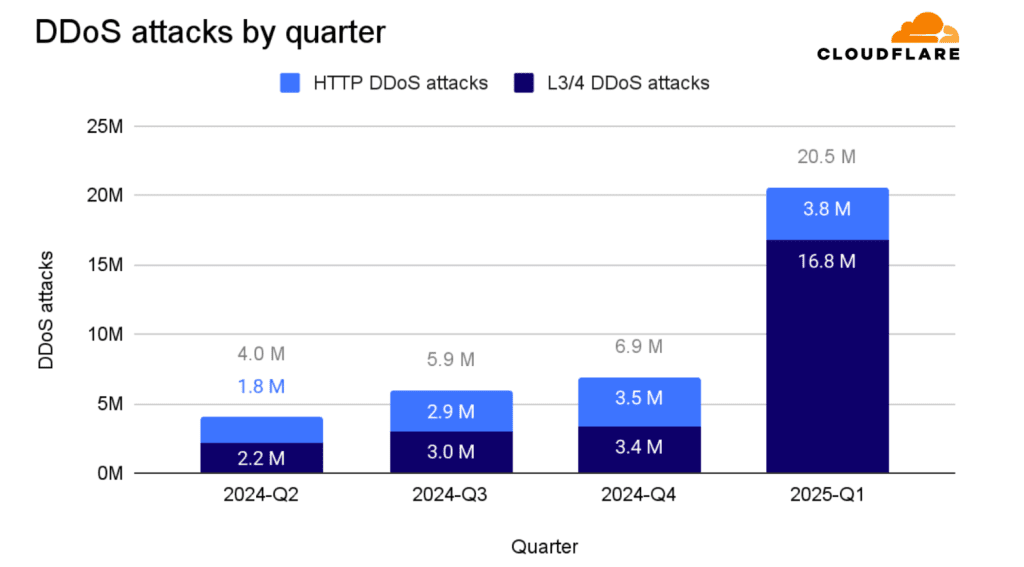
Best Practices For Mitigating & Dealing with DDoS Attacks
Hackers launch DDoS attacks to overwhelm a target’s servers, causing websites or services to crash and become unavailable.
Sometimes they do different types of DDoS attacks to demand ransom payments, threatening to keep the attack going unless paid. Others use DDoS attacks to distract security teams while they try to break into systems or to damage a competitor’s reputation.
To mitigate those multiple DDoS attack types, companies should create a multi-layered approach that combines prevention, detection, and response strategies.
Below are the best practices against DDoS attacks we recommend implementing when providing our web development services.
1. Implement Multi-Layered Protection
- Protect all layers of your infrastructure, including network, transport, and application layers, as modern DDoS attacks often target multiple layers simultaneously.
- Use specialized defenses such as Web Application Firewalls (WAFs) to filter malicious HTTP/S traffic at Layer 7.
- Incorporate robust DNS security and API protection to cover all attack surfaces.
2. Deploy Real-Time Traffic Monitoring and Anomaly Detection
- Continuously analyze network traffic patterns to detect unusual spikes or behaviors indicative of an attack.
- Use automated anomaly detection systems powered by AI and machine learning to identify slow-building or sophisticated attacks early.
- Regularly audit your network to understand normal traffic and improve detection accuracy.
3. Use Content Delivery Networks (CDNs) and Anycast Networks
- CDNs distribute traffic geographically and cache content closer to users, absorbing traffic spikes and reducing load on origin servers.
- Anycast routing helps distribute incoming traffic across multiple data centers, preventing single points of failure and improving resilience.
4. Implement Rate Limiting and Traffic Filtering
- Set request thresholds per IP or user to prevent resource exhaustion.
- Apply progressive rate limiting based on user behavior and traffic patterns.
- Use IP blacklisting and geo-blocking to restrict traffic from suspicious or high-risk sources.
5. Develop and Regularly Test an Incident Response Plan
- Prepare a detailed DDoS response plan outlining roles, communication protocols, escalation paths, and mitigation steps.
- Conduct regular simulations and drills to ensure readiness and identify gaps.
- Train IT staff to recognize attack signs and respond swiftly.
6. Design a Resilient and Redundant Network Architecture
- Use load balancers to distribute traffic evenly across servers.
- Implement failover systems and multiple data centers to maintain availability during attacks.
- Ensure cloud environments are configured for high availability and DDoS protection, leveraging services like AWS Shield, Azure DDoS Protection, or Google Cloud Armor.
7. Keep Systems and Security Measures Up to Date
- Regularly apply patches and updates to software, firmware, and security policies to close vulnerabilities.
- Stay informed about emerging threats and adjust defenses accordingly.
8. Partner with Managed Security Service Providers
- Collaborate with specialized DDoS mitigation providers who offer expertise, advanced tools, and scalable infrastructure to absorb large attacks.
- Managed services can provide 24/7 monitoring, rapid mitigation, and threat intelligence sharing.
9. Secure Infrastructure and Minimize Attack Surface
- Disable unnecessary services and close unused ports.
- Enforce strong authentication, including multi-factor authentication (MFA), to protect access to critical systems.
- Harden Windows Servers or other platforms by configuring firewalls, setting IP-based rules, and monitoring logs for suspicious activity
Here are some mitigation techniques for dealing with the most widespread DDoS attacks:
| DDoS attack Type | Description | Mitigation techniques |
|---|---|---|
| SYN Flood | Exploits TCP handshake by sending numerous SYN requests to exhaust server resources. | – Stateful firewalls and SYN cookies – Rate limiting – Traffic anomaly detection – Use of DDoS mitigation services |
| DNS Flood | Overwhelms DNS servers with massive, malformed, or legitimate queries. | – DNS traffic filtering and rate limiting – DNS firewall/protection services – Anycast DNS infrastructure |
| UDP Flood | Floods target with large volumes of UDP packets, often spoofed, exhausting bandwidth and resources. | – UDP flood detection and filtering – Rate limiting – Blocking unused UDP ports – Network ingress filtering |
| CLDAP Reflection/Amplification | Uses UDP-based CLDAP servers to amplify traffic towards the victim via spoofed requests. | – Blocking or rate limiting UDP traffic to known CLDAP ports – Disabling or securing vulnerable CLDAP servers – Traffic scrubbing via mitigation providers |
| HTTP Flood (Application Layer DDoS Attack) | Sends high volumes of HTTP GET/POST requests mimicking legitimate users to exhaust web server resources. | – Web Application Firewall (WAF) – CAPTCHA and challenge-response mechanisms – Behavioral analytics and bot detection – Rate limiting per IP/session |
| Slowloris | Opens many connections to web server and holds them open by sending partial HTTP requests, exhausting resources. | – Connection timeout tuning – Limiting concurrent connections per IP – Reverse proxies and load balancers |
| Ping Flood (ICMP Flood) | Floods target with ICMP echo requests, forcing it to respond and exhaust resources. | – ICMP rate limiting – Blocking unnecessary ICMP traffic – Network-level filtering |
| Fragmented ACK Flood | Sends fragmented TCP ACK packets causing resource exhaustion during reassembly. | – Deep packet inspection – Dropping malformed or suspicious fragmented packets – Stateful firewalls |
| Multi-Vector Attacks | Combines multiple attack types simultaneously to bypass defenses. | – Layered defense combining network, transport, and application layer protections – Use of advanced DDoS mitigation services with multi-vector detection and response |
| IoT Botnet Attacks | Uses large networks of compromised IoT devices to generate massive traffic volumes. | – Network segmentation – Blocking known malicious IPs – Collaborating with ISPs for upstream filtering – Botnet detection and mitigation |
How GitHub Recovered from a Massive DDoS Attack: Lessons Learned
The best way to avoid DDoS attacks is by learning the best practices from those who have already survived something like that. One popular denial of service attack example is GitHub’s massive DDoS attack in 2018.
GitHub faced a record-breaking attack that peaked at 1.35 terabits per second, one of the largest ever recorded.
The attack lasted about 15–20 minutes and was notable for both its size and the speed at which GitHub successfully mitigated the threat.
How the DDOS attack happened
The attackers used a memcached amplification technique, exploiting unsecured memcached servers exposed to the public internet with UDP support enabled.
They spoofed GitHub’s IP address to send small requests to these servers, and they would respond with massive amounts of data back to GitHub.
The amplification factor was huge: up to 51,000 times the original request size.
The attack came from over 1,000 different autonomous systems and 10,000+ unique endpoints, sending up to 126.9 million packets per second.
GitHub’s response and recovery
GitHub’s network monitoring systems detected the anomaly in traffic ratios and alerted their on-call engineers within minutes.
At 17:26 UTC, GitHub triggered an automated response to route all traffic through Akamai’s Prolexic DDoS mitigation service by withdrawing their BGP announcements from regular transit providers and announcing only over Akamai’s links.
Prolexic’s scrubbing centers filtered out the bad traffic and forwarded the good requests back to GitHub.
Within 10 minutes of the attack starting, mitigation was in full effect, and GitHub was mostly back up. Full recovery was within 15-20 minutes.
For several hours after the main attack, GitHub continued to route traffic through Prolexic as a precaution.
The company successfully mitigated the attack within minutes thanks to their partnership with Akamai’s security platform and their own robust mitigation strategies.
GitHub openly shared insights about their response.
They highlighted that preparation, quick detection, and collaboration with security providers helped them stay online with minimal disruption. Their transparency helped the cybersecurity community learn valuable lessons about handling huge attacks and improving resilience.
GitHub’s rapid detection and automated mitigation response were critical, reducing downtime to just minutes. This stands in stark contrast to the industry average, where DDoS detection and mitigation often take over an hour.
Following the incident, GitHub committed to expanding its edge network, increasing transit capacity, and further automating its DDoS response mechanisms to reduce future risk.
What’s Next?
Preventing DDoS requires a multilayer strategy – auditing networks and apps, leveraging provider capabilities, and implementing intelligent prevention.
As attacks rapidly evolve, expert guidance is vital.
SpdLoad provides end-to-end security services to assess risks, architect robust defenses, and respond to incidents.
Our certified team can audit your infrastructure, recommend proven solutions, and deliver ongoing management.
Contact us today for a free consultation on shoring up your DDoS defence.
Don’t let DDoS disrupt your business.
Planning your own business? Here are essential business startup tips to guide you.