About Project: Why We Stepped In
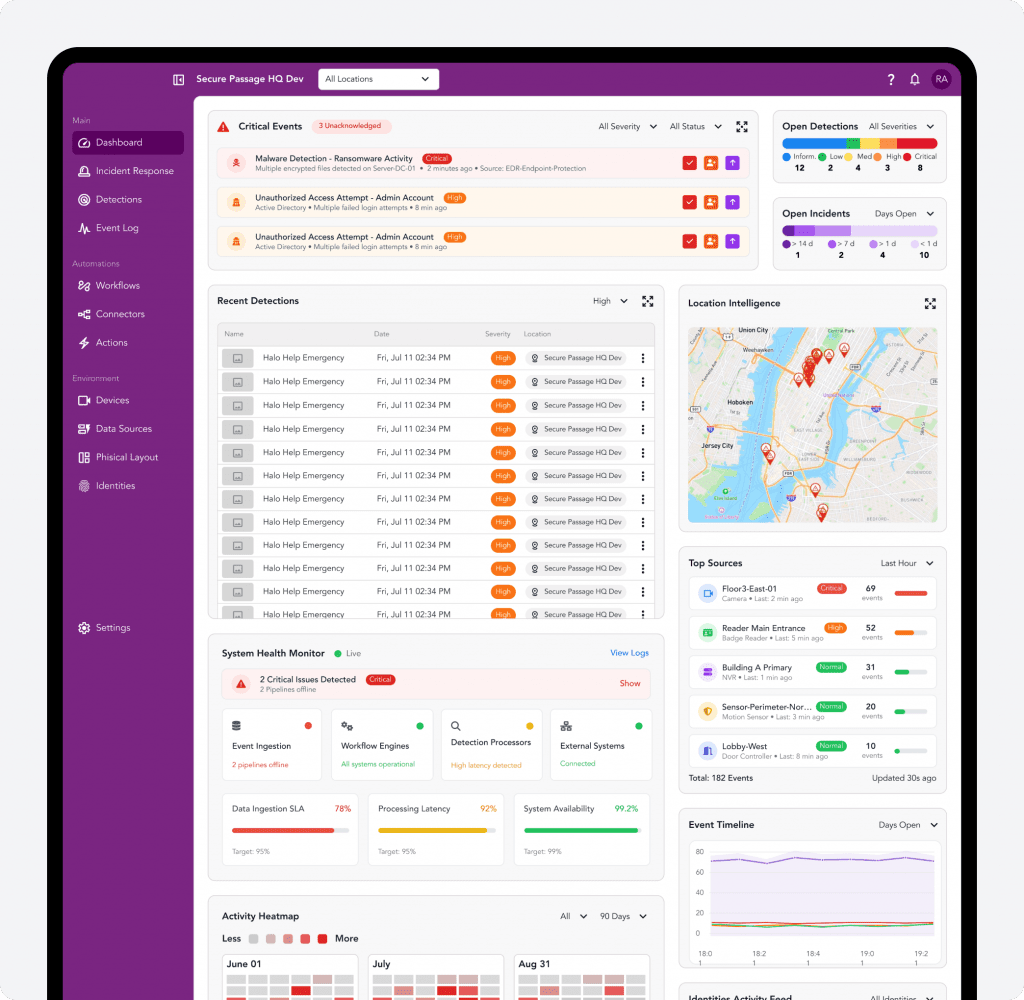
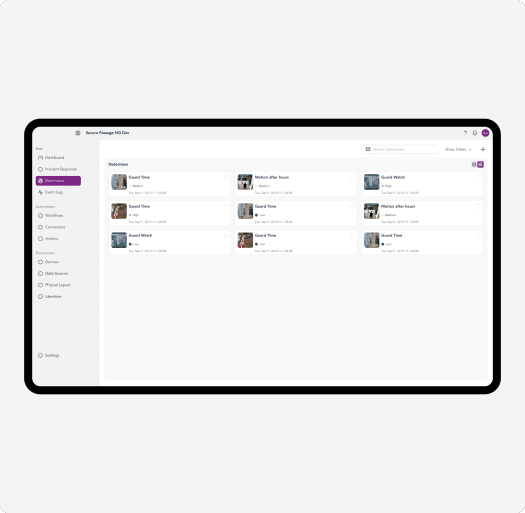
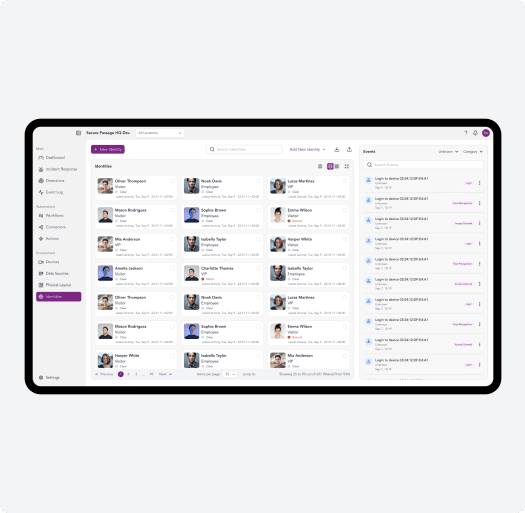
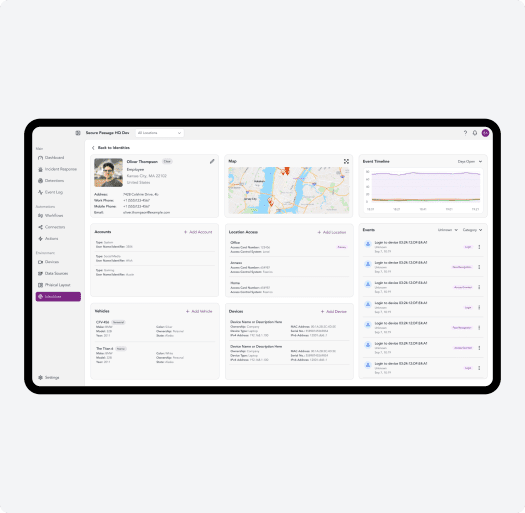
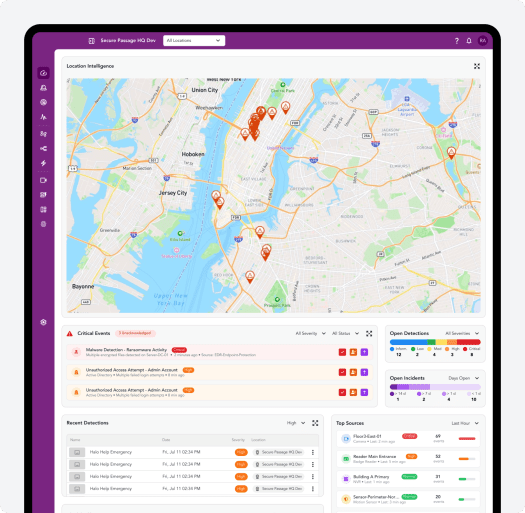
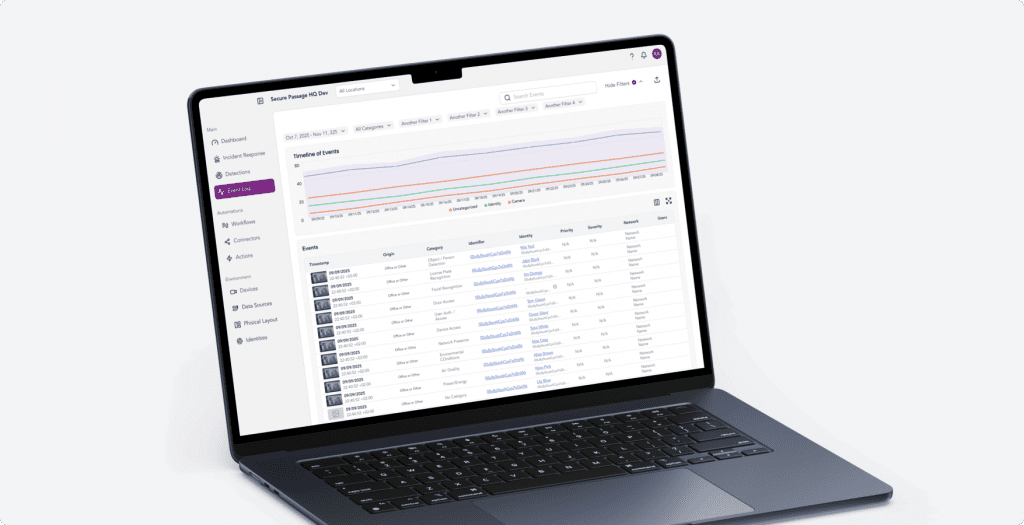
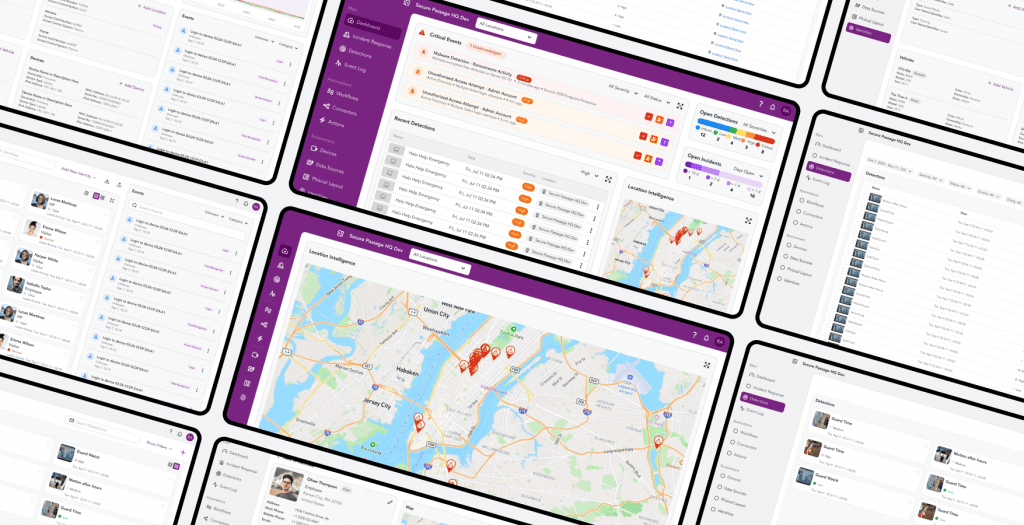
At the time our developers joined the project, the solution already existed as a group of interconnected services, including an AI-powered analytics and detection platform, rule-processing services are responsible for ingesting and evaluating events from physical devices, and a frontend service.
We stepped in to implement new features and conduct large-scale technical modernization of the platform.
The original system was built using a mix of Python, TypeScript / Node.js, and Golang, deployed on Google Cloud Platform, with Google Cloud Spanner as the primary database.
The platform is used by organizations that need to control access to facilities, manage vehicle entry and movement on secured territories, and correlate events from multiple physical security systems in real time.