IT Outsourcing Benefits, Types, and Best Practices for 2025
- Updated: Sep 23, 2025
- 11 min
The rise of advanced tech we’ve witnessed over the years drives a huge demand for tech specialists — administrators and project managers, designers and developers, testers and analysts. You name it.
So much so that the IT market’s players (agencies, e-stores, corporations, etc.) often struggle to recruit exactly the talent they need. The biggest common issue for any company with an IT department, project, or startup is gathering a multi-purpose staff that would cover most workflow aspects (if not all).
And still, various performance and productivity gaps can emerge most unexpectedly. This is where outsourcing helps a ton.
Research&Market survey indicates the global outsourcing services sector is about to reach $904.948 billion by 2027. That means more and more companies delegate their IT tasks to third-party specialists.
Businesses can outsource either the entire project, for example, mobile app development, or just parts of tasks.
Here, we dive into the benefits of IT outsourcing, its types and models, and share tips on finding the best provider of IT services.
Transform your ideas into reality with top-tier software developers — contact us to get started!
What is IT Outsourcing?
IT outsourcing is dedicating specific IT-related tasks (like software development, software testing, IT support, or data entry) to an outsourced IT team.
IT outsourcing is a perfect helping hand for a company or project that has:
- no specialist to handle a workflow aspect, use advanced technology, or offer new solutions to old issues
- not enough essential specialists on the team in general (e.g., no PM or tech lead)
- no time to fit a set deadline with existing resources
- not enough budget to finance recruitment and management of a hired dedicated development team
With IT outsourcing, you can get a competitive advantage by saving valuable time so your in-house team can focus on more critical tasks like business strategy development and client relations.
Types Of IT Outsourcing
There are more use cases and benefits of IT outsourcing, but let’s first define the basic outsourcing types you can choose to employ today.
Onshore IT outsourcing
The default, fastest, yet not the most cost-efficient option. Onshore outsourcing is when you turn to providers that are based in the same country as you are. It’s easier to connect with the providers working in the same time zone, under the same legislation, and sharing the same culture.
This must be why so many American companies readily turn to outsourcing. However, the high cost of local IT outsourcers is often the main reason why business owners and startuppers turn to outsourcing in the first place. So, this method only fits capable companies and projects.
This IT outsourcing type is great for small to medium-sized businesses (SMBs) or enterprises seeking local expertise and compliance with domestic regulations.
Onshore outsourcing is generally more expensive compared to dedicated offshore development alternatives.
Nearshore IT outsourcing
Nearshore outsourcing gives access to service providers from neighboring countries or regions. This approach combines the benefit of proximity with potential cost savings. Are local IT service prices overly expensive?
You may find a much better-priced option delivered at the same level of quality in a country that isn’t too distant and culturally different. That is, if you do have such a neighbor, and they have a well-developed IT market.
This IT outsourcing type can benefit companies located in regions with limited local resources or seeking cost-effective solutions without compromising proximity.
Offshore IT outsourcing
You can delegate work to specialists in distant regions, tapping into wider talent pools at lower labor costs. Yes, it may come with its own challenges (language, time zone, etc.). But an offshore approach pays off tenfold if you know where to look, prepare, and partner up with a reliable provider.
Successful apps are often the result of strong partnerships. Learn how to build one in our article on app development partnerships.
Large enterprises and global corporations, as well as startups who are seeking highly skilled specialists at affordable rates, can use this IT outsourcing model.
Now, let’s wrap up and compare these three IT outsourcing types:
| Aspect | Onshore outsourcing | Nearshore outsourcing | Offshore outsourcing |
|---|---|---|---|
| Average hourly rate | $100−$200 | $50−$100 | $20−$50 |
| Average monthly cost (FTE) | $15,000−$30,000 | $7,500−$15,000 | $3,000−$7,500 |
| Cost efficiency | Highest cost | Moderate cost | Lowest cost |
| Time zone alignment | Same time zone | 1-3 hours difference | 6-12 hours difference |
| Cultural alignment | High cultural similarity | Moderate cultural similarity | Low cultural similarity |
| Language proficiency | Native language | High proficiency (often bilingual) | Moderate to high proficiency (may require additional communication effort) |
| Examples of locations | USA, UK, Germany | Mexico (for USA), Ukraine (for Western Europe) | India, Philippines, Vietnam |
Models of IT Outsourcing
No matter how far your outsourced workforce is located, they are usually ready to collaborate based on one of the following models.
Project-based IT outsourcing
In the project-based outsourcing model, companies/projects turn to external service providers to complete specific projects or tasks within a defined scope and timeframe.
This model is perfect when you are looking for some short-term initiatives to fix some gaps in a well-planned project quickly. For example, when you have a running workflow yet struggle with a certain metric that requires some narrowed-down expertise (e.g., BI analytics).
Dedicated team model
With the dedicated model, you can hire a full-stack or custom team of professionals to work exclusively for your needs.
Naturally, this gives more control over workflow management and resource allocation. Outsourcing providers usually offer team leads and project managers from their talent pool, with the option of retaining your own PM if you already have one.
Outstaffing model
Outstaffing allows you to introduce outsourced specialists to your existing team as full-on members.
But only for now – you basically “rent” the workforce, saving tons on recruitment and employment. Even better, you can let go of outstaffed workers whenever needed without firing anyone. This is an excellent option for small businesses looking to scale and complete industry-specific tasks without hiring expensive professionals full-time.
The top priority here is the smooth integration of in-house and outsourced IT teams (explore the difference between in-house development vs outsourcing).
Business Process Outsourcing (BPO)
While not strictly IT-focused, BPO involves outsourcing non-core business functions.
This includes IT-related processes such as data entry, customer support, and back-office operations.
BPO and information technology outsourcing (ITO) are closely linked because many business processes rely on technology.
Together, they generated $92.5 billion in 2019, according to Statista.
Regardless of the model you choose, IT outsourcing offers businesses flexibility, access to specialized expertise, and cost savings.
It enables companies to focus on their core competencies and strategic objectives.
This leads us to the next point of this article, which is the benefits of outsourcing. 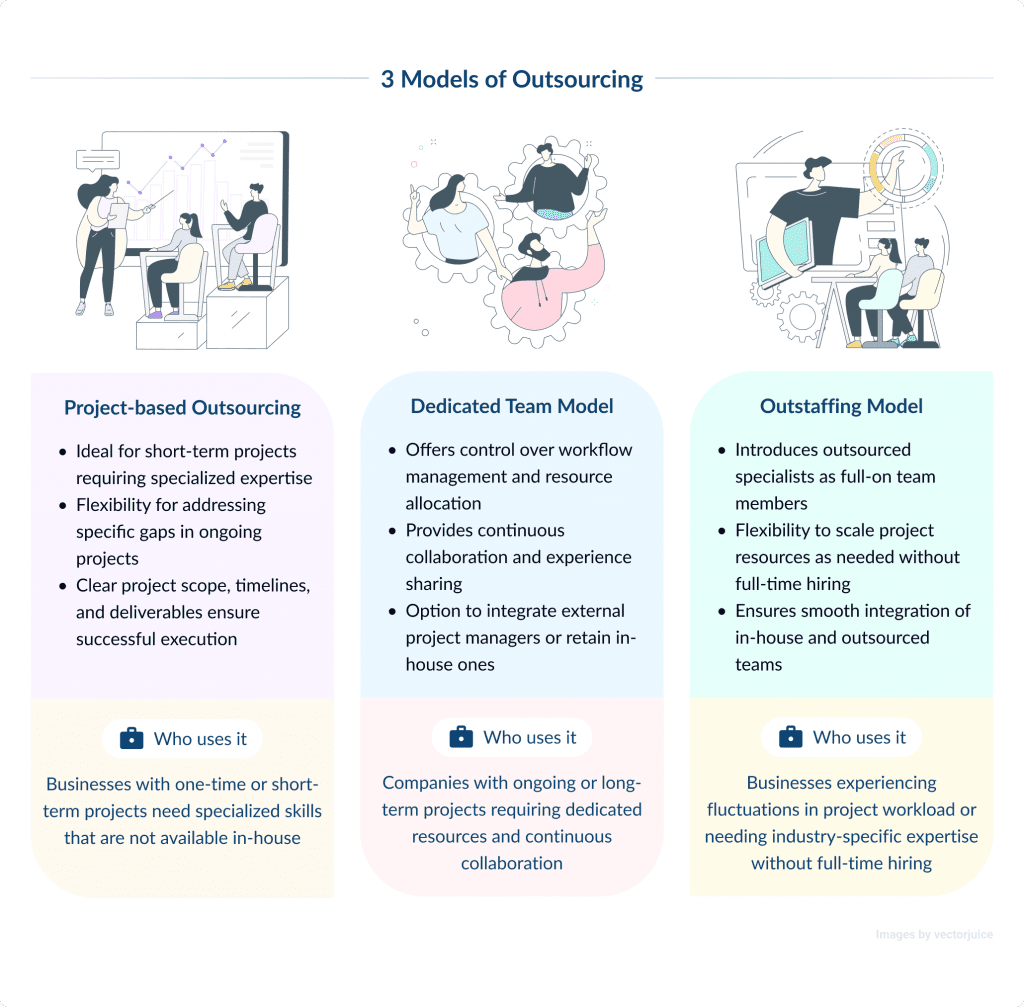
Unlock the power of WordPress with our experts.
IT Outsourcing Advantages
Now, let’s see some reasons to go for outsourcing in the first place.
- IT outsourcing comes at variable costs that can cater to both small ventures and large companies. You can expect to save up to 40% of your normal IT maintenance budget.
- The outsourced team gives you well-tried, carefully pre-screened specialists with a skill set that matches your requirements.
- A small business can offload routine tasks in favor of focused performance for better business outcomes. Learn more about IT outsourcing for small business.
- Outsourcing is a real remedy for projects running on a tight schedule. II is an arena of rapid technological evolution and ever-shifting demands, and missed deadlines can cost too much.
- Project delays, hidden costs, security breaches, and failed ROI are common risks to tackle via outsourcing.
- Freed-up internal IT staff can be invested in customer experience, satisfaction, and loyalty. For instance, an e-commerce company can adopt a customer-centric approach to retain customers and grow revenue. Want to join the booming eCommerce market? Learn how to develop an eCommerce app that meets customer needs.
While there are many IT outsourcing benefits, be prepared for the following challenges. 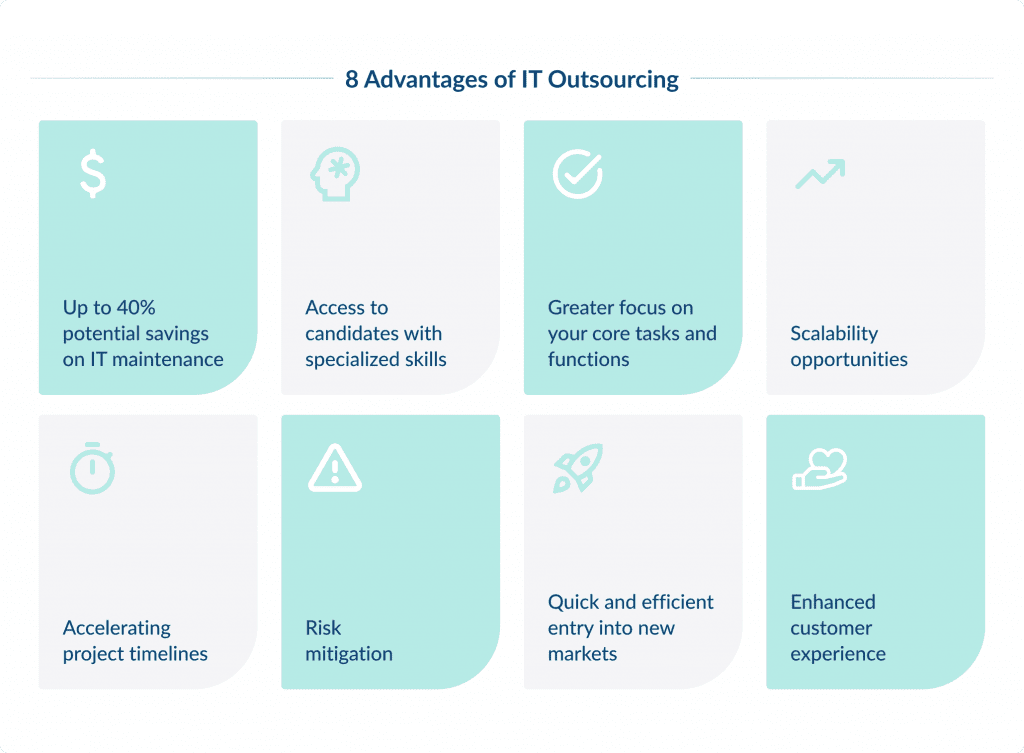
Finding a reliable outsourced IT team
If you have an in-house team, you most probably trust these people. They know all the specifics of your company and your business goals and manage your valuable corporate data responsibly. How can you be sure about that when it comes to an external team? Will your business idea and intellectual property be safe?
There are all reasonable concerns. At SpdLoad, we always offer our potential clients to sign an NDA to safeguard your business idea and other valuable information. Also, you can freely explore reviews from our clients on Clutch to see if our services and collaboration practices match your needs.
Also, check if the information technology outsourcing company is extra diligent about following regulations like ISO/IEC 27001 (an international information security requirements standard) and GDPR (when you tap into European outsourcing markets).
Sometimes, it can take time to find an outsourcing company you can trust, but it is always worth the effort.
Ensuring quality of services provided
It’s challenging to be completely confident in the quality of work your newly hired external service provider delivers. It’s natural to wonder, “Will they deliver the quality we need?”
The good news is that reputable outsourcers usually have Clutch reviews and ratings, offer contract-based partnerships, and consult with you throughout the process.
Another way they build confidence is through a well-rounded collaboration agreement. A solid contract should outline scope, timelines, deliverables, and quality benchmarks to eliminate guesswork.
Plus, experienced providers will usually highlight that they follow strict processes, like Agile methodologies or ISO standards, to deliver high-quality software and IT infrastructure solutions.
Communication is also key. At SpdLoad, we keep our clients in the loop with regular updates, progress reports, and check-ins.
Cost overruns
Cost overruns can quickly turn a well-planned project into a financial headache. This can happen due to unexpected issues or poor budget planning. It also depends on the IT outsourcing pricing model you choose. This is especially the case for the fixed price model, as it lacks flexibility.
Based on our business practice, the time and material pricing model is one of the best suited for IT outsourcing. Before the collaboration starts, we provide a thorough project estimate, and after the client approves it, we launch the development process. The estimate takes us around two business days and it is absolutely free.
3 Best IT Outsourcing Countries
Based on stats, market research, and experience over the years, we can identify these top outsourcing destinations for 2025.
Ukraine – Leading IT Outsourcing Country
Ukraine remains a top IT outsourcing services provider. The country offers high-quality work at competitive rates. It has a billion-worth IT outsourcing market that’s projected to hit over two billion by 2028. There’s a huge pool of professionals, a favorable business environment, and a strong educational system.
Ukrainian software developers create unique projects like Grammarly and People.ai, not to mention all the Facebook and Google employees hailing from the country. There are plenty of highly educated, skilled IT specialists, so the competition is always on, which means their rates remain reasonable.
The IT industry pool counts up to 170,000 IT specialists available for hire. Most speak English fluently, and 50% of specialists possess a STEM education degree. This is the highest level of proficiency in the Eastern European region. IT outsourcing rates in Ukraine are around $40 per hour. 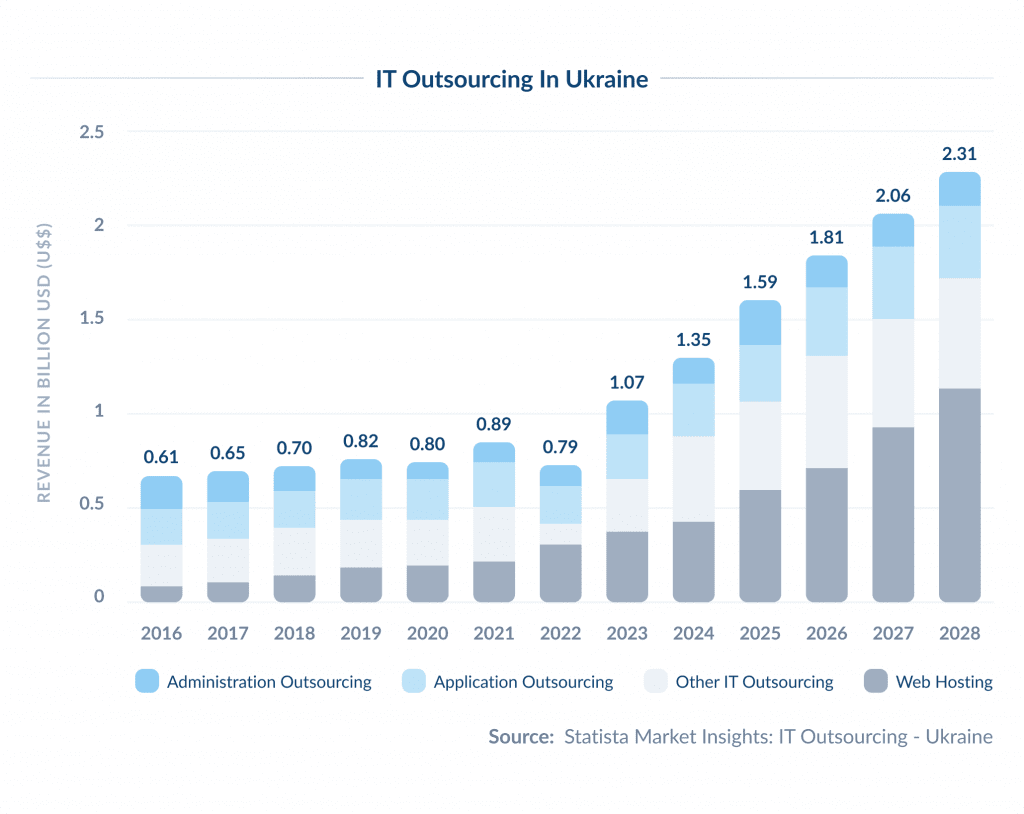
Poland – Good Services at High Prices
A Central European IT outsourcing leader. The only downside is that the cost of a Polish IT specialist’s hours is one of the highest in the region, reaching $99 per hour. The local outsourcing industry employs 250,000 professionals.
With a high level of English and proximity to Western Europe, Poland offers a proven and stable outsourcing option. However, their rates might be too high for small businesses, startups, and anyone looking for cost reduction opportunities.
The Philippines – Emerging IT Outsourcing Provider
The Philippines is an emerging outsourcing destination where the market is yet to ripen, but you can easily acquire your own team at more than competitive rates. Opting for a growing market can be a surprisingly efficient choice. There is a 0.79-billion-rich IT segment with steady growth. And while the top-level talent pool may be scarcer there, it costs an average of $15-45 per hour.
The final cost of outsourcing a project is very individually shaped. The decisive factors include:
- Service outsourcing company location. Explore the best countries to outsource software development.
- Level of required expertise
- The overall complexity of the workflow
- Duration of IT outsourcing partnership
- Technological requirements for an outsourced team
Level up your team with Node.js development specialists
IT Outsourcing Best Practices
Did you know that 78% of companies that outsource enjoy working with their outsourcing partners? However, finding a reliable and trustworthy outsourcing provider is harder than it seems. Here are some IT outsourcing best practices to help you get through the process:
Set clear objectives
Before you outsource, define your goals. What do you want to achieve, and how does outsourcing fit into your business strategy?
Without clear objectives, you’ll run into problems down the track.
Choose a compatible provider
Look beyond technical skills. Make sure your service provider fits your company culture, business objectives, and working style. They should slot into your organization like an actual employee would.
Think long term
Don’t just focus on short-term cost savings.
Consider the long-term impact of outsourcing. What are the desired outcomes beyond the initial deal? Keep the big picture in mind.
The Rise of AI-Powered Outsourcing
AI-powered outsourcing is when companies dedicate part of the tasks to AI tools instead of putting them on the shoulders of in-house teams or outsourcing companies. This practice is also called Outsourcing 2.0.
Deloitte’s Global Outsourcing Survey highlights that AI-enabled workers and automation bots are getting popular. 83% of surveyed executives noted that they actively use AI as part of their outsourced services, and 20% are already developing strategies to manage these digital workers.
Undoubtedly, this new type of outsourcing business model can seem like an attractive option: it is cheaper, available round the clock, and responds in seconds. And with built-in learning, AI systems will only improve their performance over time.
Many industries are already benefiting from AI automation. For example, insurance automation helps to speed up claims processing, provide a more customer-centric experience, boost productivity in insurance processes, and reduce operational expenses.
The rise of AI in healthcare can potentially change population health management and healthcare delivery. Many healthcare providers already use machine learning, natural language processing, computer vision, AR/VR, and robotics. These innovative tools help to manage health records, educate patients and healthcare professionals, speed up treatment discovery, and even assist in surgeries.
Despite all these benefits, outsourcing software development and other IT-related services to AI is still risky. AI solutions are hard to manage, they are prone to errors and require a human hand to control their “work” thoroughly.
At this point of AI development, it is much better to rely on the outsourced team rather than putting your tasks into artificial intelligence. I believe that traditional outsourcing will continue as organizations leverage the skills of dedicated IT services companies for many critical tasks, allowing them to focus on the core business.
Organizations must collaborate closely with vendors to fully realize AI’s potential, establish robust AI governance, develop comprehensive digital workforce strategies, and identify and implement AI use cases.
Bottom Line
The question remains: Is outsourcing the right choice for your company?
Well, considering all the advantages we’ve covered above, it might be a reasonable choice for you.
Outsourcing allows you to delegate IT tasks to experts who can handle them better, faster, and at a more affordable cost. However, we understand that you might need more time to select a reliable IT outsourcing partner.
At SPDLoad, we’ve got you covered. We value our strong client relationships and are committed to delivering the best results for everyone. We understand that every situation is unique, especially regarding IT challenges and struggles.
Transitioning from in-house to outsourcing can be challenging, but you can always rely on our expertise and over 10 years of experience developing innovative SaaS solutions.
If you’re deciding between software models, this comparison of the ASP model vs SaaS model can help you choose.
Connect with one of our specialists today to explore how SPDLoad can assist you. We’ll work closely with you to understand your needs and develop a tailored outsourcing solution.